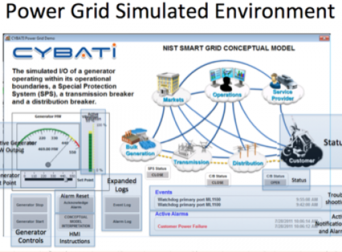
The internet of things digital factory industry 4 0 and all of the new strategies for improving manufacturing and production efficiencies contain a common element.
Ics cyber security best practices.
The cybersecurity and infrastructure security agency cisa mission is to promote a cohesive effort between government and industry that will improve cisa s ability to anticipate prioritize and manage national level ics risk.
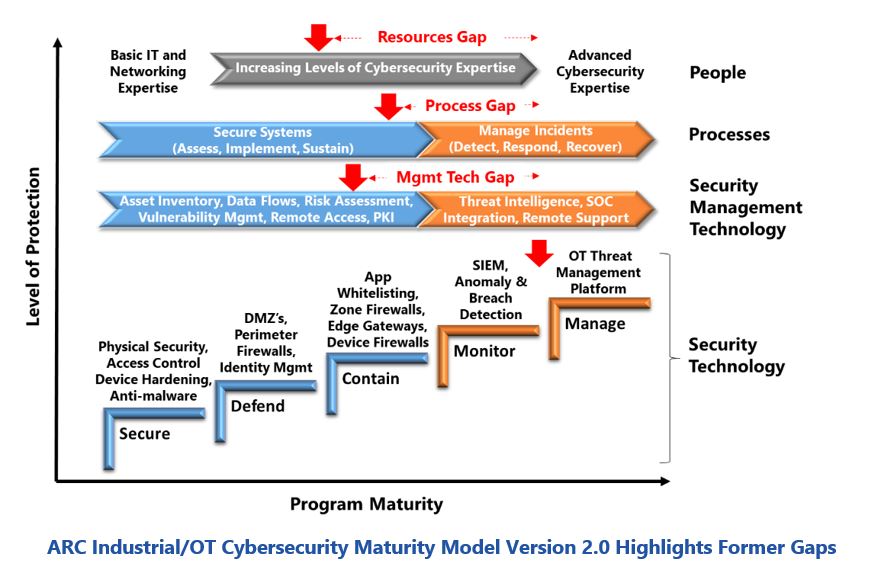
Updates to security capabilities and tools for ics.
9 best cybersecurity practices for the it ot environment in the world of cybersecurity there is no silver bullet.
Scammers can fake caller id information.
Industrial control system ics cybersecurity advice best practices catastrophic disaster can be the result of insecure industrial cybersecurity practices.
Cybersecurity best practices for industrial control systems ics owners and operators face threats from a variety of adversaries whose intentions include gathering intelligence and disrupting national critical functions.
Secure online experience cis is an independent non profit organization with a mission to provide a secure online experience for all.
Comprehensive ics cyber security best practices white paper.
This page provides abstracts for existing recommended practices and links to the source documents.
The cybersecurity and infrastructure security agency cisa the department of energy doe and the uk s national cyber security centre ncsc have released cybersecurity best practices for industrial control systems an infographic providing recommended cybersecurity practices for industrial control systems ics the two page infographic summarizes common ics risk considerations short and.
Our security best practices are referenced global standards verified by an objective volunteer community of cyber experts.
The cisa assists control systems vendors and asset owners operators to identify security vulnerabilities and develop.
New tailoring guidance for nist sp 800 53 revision 4 security controls including the.
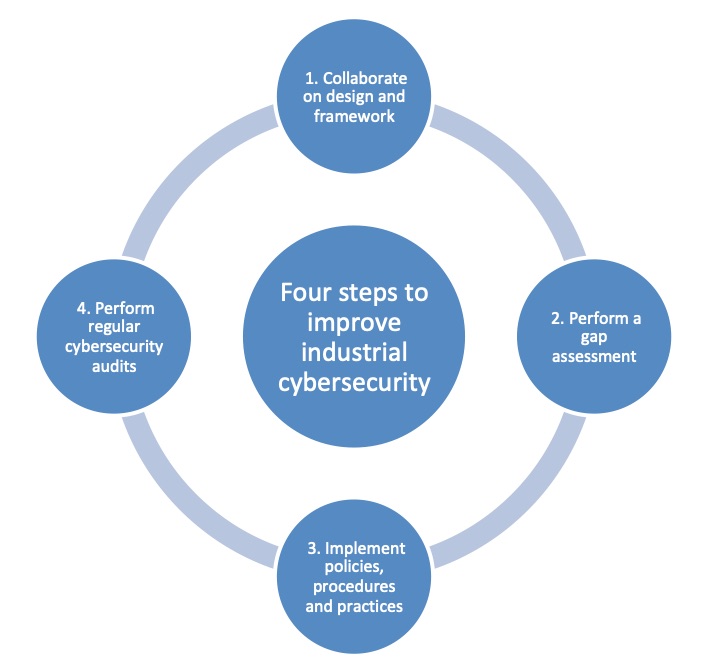
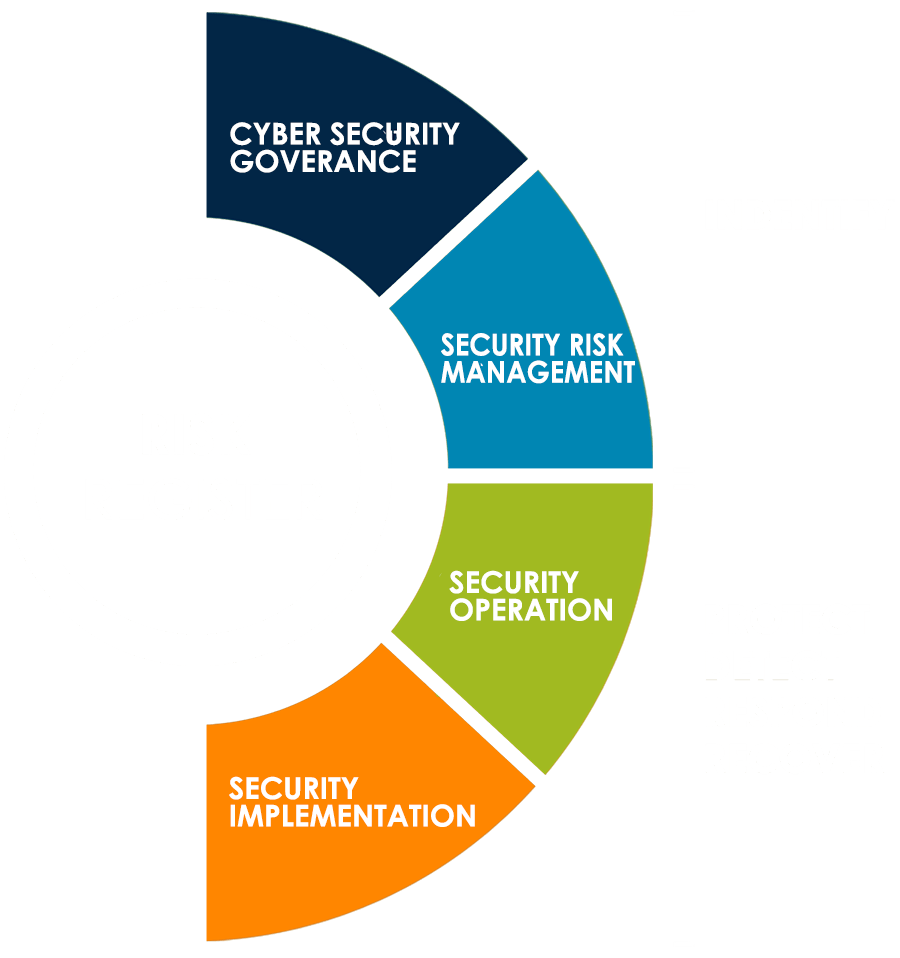
See six common entry points for attacks eight cybersecurity precautions for attacks by type and four steps to improve.
By gary mintchell jan 16 2018 automation security 0 comments.
Additional alignment with other ics security standards and guidelines.
What you can do in your organization is to minimize the attack surfaces and threat vectors and be vigilant and proactive in your defense against adversaries.
Updates to ics risk management recommended practices and architectures.
Cybercriminals can create email addresses and websites that look legitimate.
If you work for a small or midsize company it s smart to learn about cybersecurity best practices.
Additional supporting documents detailing a wide variety of control systems topics associated with cyber vulnerabilities and their mitigation have been developed and vetted by control systems smes.